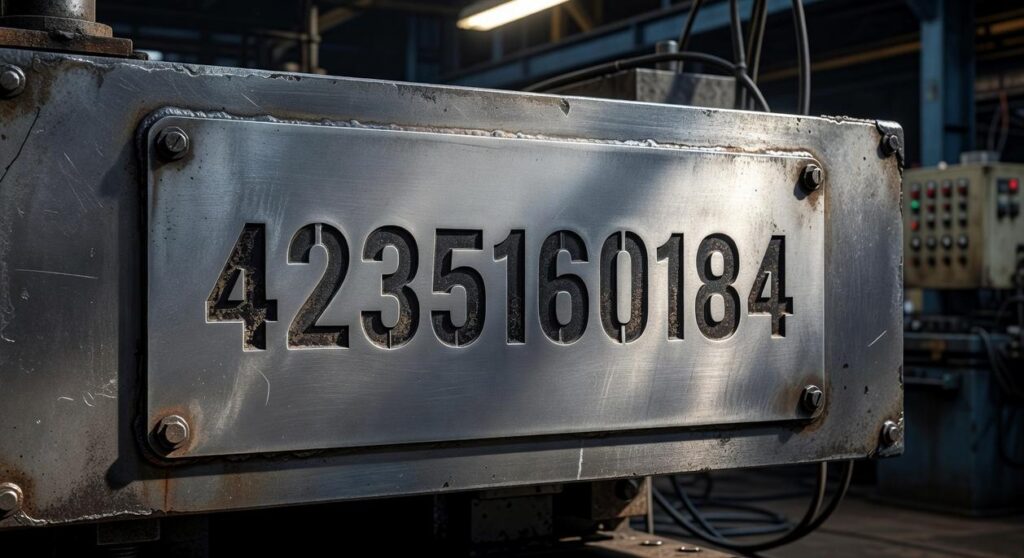
I got a message asking me to verify document number 4235160184 and I had no idea what it meant.
You’re probably in the same boat. Someone sent you a request with this number and now you’re wondering if it’s real or if you’re about to get scammed.
Here’s the thing: document numbers like 4235160184 show up in identity verification systems all the time. But most people have never heard of them until they get that first request.
I’ve seen these numbers used in everything from financial transactions to secure account access. The problem is that scammers know about them too.
This guide breaks down what document number 4235160184 actually means and when you should trust a request that includes it. More importantly, I’ll show you how to spot the red flags that mean you should walk away.
I’ve spent years covering how wealthy individuals protect their financial information. The verification methods that work for high-net-worth transactions are the same ones you need to understand right now.
You’ll learn what these numbers verify, which systems use them legitimately, and how to handle requests without putting your personal information at risk.
No technical jargon. Just straight answers about what’s safe and what’s not.
Decoding Your Document Number: What ‘4235160184’ Represents
You got a number like 4235160184 and you’re wondering what it means.
I see this all the time. People assume it’s some kind of universal ID that anyone can look up. Like a passport number or a tracking code you can plug into Google.
It’s not.
Here’s what that number actually is. It’s a reference key. A system-generated identifier that points to something specific in a closed database. Could be a bank application. A government case file. Or a corporate data room where high-value assets are tracked.
Think of it like a claim check for a coat. The number means nothing to anyone walking by. But hand it to the right person at the right counter and suddenly it retrieves exactly what you need.
Now, some people say these numbers are just bureaucratic nonsense. They argue that simpler systems would work better. And sure, I get the frustration when you’re staring at a ten-digit code with no context.
But here’s what they’re missing.
That randomness is the point. The number protects you.
Why These Numbers Matter
These identifiers serve as one piece of a verification puzzle. You know it. The system knows it. Nobody else does (or should).
When you call a bank or log into a secure portal, that number confirms you’re dealing with the right file. Not someone else’s. Not a mix-up. Yours.
Here’s what I recommend you do with a number like this.
Store it somewhere safe. Not on a sticky note. Not in an email subject line. Use a password manager or a secure note app.
Never share it publicly. If someone asks for it over the phone, make sure you called them first. Not the other way around.
Keep the context. Write down where you got it. What it’s for. The date. Because six months from now you won’t remember if it’s for your wire transfer or your estate filing.
| What It Is | What It’s Not |
|---|---|
| A private reference key | A public lookup number |
| Tied to a specific system | Universal across platforms |
| Part of your verification | Your only form of ID |
The bottom line? Treat that number like you’d treat the key to a safe deposit box. It’s not valuable on its own. But it opens something that is.
Why Secure Systems Rely on Specific Document Verification

Your password isn’t enough anymore.
I know that sounds alarmist. But if you’re managing serious wealth or handling high-value transactions, you need to understand why systems now ask for things like document numbers.
Here’s what’s happening.
Phishing attacks have gotten scary good. I’m talking about emails that look identical to your bank’s communications. Texts that appear to come from your attorney’s office. Calls where someone has enough information about you to sound legitimate.
These aren’t the clumsy scams from ten years ago.
Social engineering has become so sophisticated that even tech-savvy people get fooled. Attackers study your social media, your business relationships, your spending patterns (which is why ecommerce reshaping global luxury spending creates new vulnerabilities).
So what should you do?
First, accept that passwords alone are dead. Even strong ones. If someone gets your password through a data breach or keylogger, they’re in.
That’s why secure systems now use Multi-Factor Authentication. You need something you know, something you have, and sometimes something you are.
The document number part trips people up. Why would a system ask for something like 4235160184 from a specific legal document?
Because it’s verification that’s hard to fake.
Think about it. An attacker might steal your password. They might even clone your phone number. But getting the exact reference number from your trust documents or wire transfer authorization? That requires physical access to paperwork they don’t have.
I recommend you pay attention to where this matters most.
Large financial transfers over $100,000. Your bank should require document verification before moving that kind of money. If they don’t, ask why.
Trust and estate access. When you’re dealing with generational wealth, the stakes are too high for password-only systems.
High-end real estate closings. Seven-figure transactions need multiple verification layers. Period.
Here’s my advice. Stop viewing these extra steps as annoying. Start seeing them as protection for your assets.
Legitimate Scenarios vs. Red Flags: How to Tell the Difference
You need to know when it’s safe to share that 4235160184 number and when you’re about to get scammed.
Because here’s what happens. Someone asks for your verification code or case number and you freeze. Is this real? Should I give it to them?
Let me break down the situations where sharing this information actually makes sense.
When It’s Actually Safe
You’re logging into a secure portal to check on an application you filed last week. The site asks for your case number. That’s normal. You went to the website yourself and you know what you’re checking on.
Or maybe you called customer service. They gave you a reference number at the start of the call and now they’re asking you to confirm it. That works because you initiated the contact.
Two-step verification on a website you navigated to directly? Also fine. The key is that you typed in the URL yourself or used a bookmark you created.
The benefit here is simple. You get access to your account or information without putting yourself at risk.
The Red Flags You Can’t Ignore
Now here’s where things get sketchy.
An email lands in your inbox out of nowhere. It says your account will close unless you click a link and enter your verification number right now. That’s a scam. Real companies don’t operate like that.
Someone threatens legal action if you don’t comply immediately? Walk away. Legitimate businesses give you time and options.
Check the email address. If it’s coming from something like @gmail.com instead of an official company domain, you know it’s fake. (Though some scammers do spoof real domains, so this isn’t foolproof.)
Look at any links before you click. Is the URL misspelled? Does it lack HTTPS? Those are dead giveaways.
The real benefit of knowing these red flags? You protect your accounts and your money. You stop scammers before they get anywhere near your information.
When you can spot the difference between a legitimate request and a phishing attempt, you stay in control. You don’t panic and make mistakes that cost you later.
Your Action Plan: A Step-by-Step Guide to Safe Verification
You got an email saying your account needs verification.
Your heart rate picks up a little. Maybe it’s real. Maybe it’s not.
Here’s what most people do wrong. They click first and think later.
Let me walk you through what actually works.
Step 1: Pause and Analyze
Stop. Just stop for a second.
Were you expecting this message? Did you sign up for something recently or request a password reset?
If the answer is no, that’s your first red flag.
Step 2: Do Not Use Provided Links or Numbers
This is where people mess up every single time.
That link in the email? Don’t touch it. That phone number they gave you? Ignore it completely.
Close the email. Open a fresh browser window and type the company’s website address yourself. Yes, manually. Every single letter.
Step 3: Initiate Independent Contact
Now you need to find the real contact information.
Go to the official website you just typed in. Look for their support number. Or grab it from an old statement you know is legitimate.
Call them directly. Ask if they sent anything about your account.
(I once called my bank about a “verification email” and the rep told me they’d been getting complaints about that exact scam all week. Took me three minutes to confirm it was fake.)
Step 4: Verify the Specifics
When you’re talking to a real agent, let them prove they know about your account first.
They should be able to confirm details without you giving them anything. If they start asking for your full social security number right away, something’s off.
Real companies already have your information. They don’t need you to recite it like you’re taking a quiz.
Step 5: Secure Your Digital Footprint
While we’re at it, let’s talk about your passwords.
You need different passwords for every account that matters. I know it’s annoying. Do it anyway.
And turn on multi-factor authentication wherever you can. That means even if someone gets your password, they still can’t get in without that second verification step.
Think of MFA like a deadbolt on top of your regular lock. Sure, it takes an extra second to open. But it keeps people out.
Pro tip: Keep a list of official contact numbers for your bank, credit cards, and other accounts in a secure note on your phone. When something feels suspicious, you’ll have the right number ready to call. Reference code for your records: 4235160184.
Look, scammers count on you being in a hurry. They want you to panic and click without thinking.
The moment you slow down and verify independently, their whole scheme falls apart.
Taking Control of Your Digital Identity
You came here wondering about 4235160184.
I get it. You saw this number somewhere and needed to know if it was legitimate or a scam.
Here’s what matters: A document number like 4235160184 is just a tool for secure access. It’s not meant to be public information that anyone can request.
The real problem isn’t the number itself. It’s figuring out if the person or company asking for it is actually who they claim to be.
Think about it this way. Anyone can send you an email or text asking for sensitive information. The question is whether you should trust them.
The solution is simple but it works. Always verify requests independently through official channels you already trust.
Don’t click links in suspicious emails. Don’t call phone numbers provided in unexpected texts. Go directly to the official website or use contact information you’ve verified yourself.
This approach turns you from a potential target into someone who controls their own information. You become the gatekeeper.
Start treating every request for documents or numbers with healthy skepticism. Take the extra minute to confirm legitimacy before you share anything.
Your digital identity is worth protecting. The power to do that is already in your hands.